"App shielding solution AppCAMO protects Android native apps such as Java and Kotlin, and Cross-Platform apps(hybrid apps) such as Cordova, Ionic, React Native, and Cordova extensions against reverse engineering and tampering."
From August 2021, when distributing new
Android apps to Google Play, Google changed the app policy so that it can only
be uploaded using the new app file format, AAB, rather than the existing APK,
which is the existing app file format.
 |
| Fig. 1 Android App security - APK file architecture |
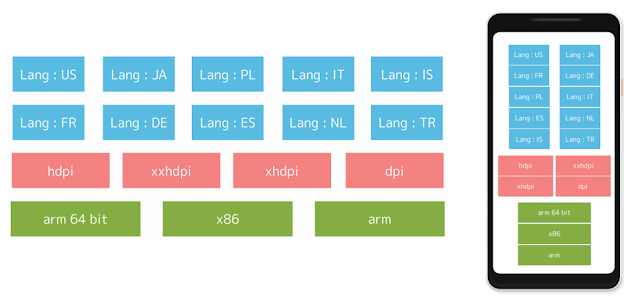
APK file size continues to increase
Currently, APK files have a single
architecture called "FAT Binary", supporting multiple devices with
different CPUs(ARM, ARM64, x86, etc).
The APK file size is inevitably increased
over time due to the addition of high-definition resources for supporting new
devices or high-resolution hardware, and the addition of language sets for
multi-language support.
 |
| Fig. 2 Android App Shielding - AAB file architecture |
Recommend AAB file format to solve APK file
size issue
In 2018, Google analyzed the correlation
between APK size and installation rate and announced that for every 6MB
increase in APK size, the percentage of users installing apps dropped by 1%.
Google recommended the AAB file format to
solve this APK file size issue.
If the developer builds the app as an AAB
file and distributes it to Google Play, the APK file optimized for the user's
device can be downloaded, reducing the app size, download time, disk allocation
size, and installation time.
 |
| Fig. 3 AAB file architecture and contents |
Base APK: Essentials to run an app
Configuration APK: CPU, screen density, and
language classification
Dynamic Feature APK: Focus on features for
small users or infrequently used add-ons
Asset Pack APK: Focus on features that
require a lot of graphics, such as games
BUNDLE-METADATA: Metadata that includes
useful information related to Google Play, including ProGuard mapping
information and full DEX file list information.
Module protocol buffer (*.pb) file: Metadata
that helps to describe the contents of each app module on Google Play, and
provides information necessary to generate an APK optimized for the device.
App Security Solution AppCAMO protects AAB
file
AppCAMO’s AAB protection technology
provides more than 20 security technologies that comply with OWASP(Open Web
Application Security Project), the same as AppCAMO’s APK protection technology.
And, it consists of static analysis prevention(Code Hardening) technology and
dynamic analysis prevention(RSAP: Runtime Application Self Protection)
technology.
Static analysis prevention(Code Hardening) protects
AAB files from hacking.
decompile prevention,
repackaging prevention,
class name obfuscation,
method name obfuscation,
field name obfuscation,
code encryption,
string encryption,
resource encryption,
hybrid app Encryption(JavaScript encryption,
WebView encryption);
custom hybrid app encryption(custom webview
encryption);
debug information removal,
Logcat log removal, and more.
Dynamic analysis prevention(RASP) blocks
hacking attempts while an app is running.
tampering detection,
debugger detection,
root detection,
emulator detection(Virtual Machine
detection);
root hide detection(Magisk/Magisk
Hide detection);
Hacking tool detection(Frida detection),
API hooking prevention,
memory hack prevention,
screen capture prevention,
clipboard copy protection,
Usage time control, and more.
AppCAMO provides the same app protection technology for AAB file as well as APK file of Android app.
"App security solution AppCAMO provides multi-layered protection technology that strongly blocks app hacking, and has world-class app security technology by providing app hacking detection and prevention technology even at runtime. We are expanding our sales not only in Korea, but also in overseas markets such as Southeast Asia and the United States."
If you are interested in this solution or have any questions, please feel free to contact us below.
Email : appcamo@appcamo.com
www.appcamo.com







