"Mobile apps are very vulnerable to hacking because the source code of the app is easily exposed as a decompilation tool (reverse engineering tool). AppCAMO-iOS protects iOS apps safely by thoroughly blocking hacking through static analysis prevention(Code Hardening) and dynamic analysis prevention(RASP : Runtime App Self-Protection) technology of AppCAMO-iOS when hackers attempt hacking using static analysis and dynamic analysis."
 |
| Fig. 1 iOS App Shielding Solution AppCAMO-iOS Security technologies |
iOS app Vulnerabilities
iOS is known to be secure as Apple fully owns its security controls, but it turns out that iOS has more security vulnerabilities than Android. And iOS jailbreak cases by hacking continue to increase. So, the assumption that iOS apps run in a secure environment can be risky.
iOS security problems mostly occur on jailbroken iOS devices, and it is possible to access system files inside iOS and control them remotely.
iOS apps are less secure than Android apps, and 40% of vulnerabilities found are fatal or severe, higher than Android's 36% (Checkmarx & AppSec Labs).
A study of the top 100 paid iOS apps in the Apple App Store found that 87% of them were hacked, 75% of the popular free iOS apps were hacked, and the percentage of popular iOS apps hacked has continued to rise over the past three years (ARXAN ).
 |
| Fig. 2 Why you need iOS app security ? |
Attack cases such as tampering iOS apps and infecting them with malware were discovered, and it was confirmed that the game Pokemon Go, which recorded 500 million downloads worldwide, also has an iOS cracked version in circulation.
AppCAMO protects iOS apps from hacking and reverse engineering through Code Hardening and Runtime App Self-Protection (RASP) mechanisms. Since most app security solutions are SDK-based, learning time and coding are required to apply security technology to the app, but AppCAMO is web GUI-based, so you can easily apply app security technology with simple clicks.
The most powerful mobile application protector against hacking
AppCAMO-iOS is one of the most powerful app shielding solutions that block hacking by applying various app security technologies hierarchically from hacking threats caused by reverse engineering and tampering.
AppCAMO-iOS is easy and convenient to use because you can select and apply security options with just clicks of the app security technologies on the web browser after uploading the Xcarchive file.
 |
| Fig. 3 iOS app security solution AppCAMO-iOS architecture |
14 powerful app security technologies
AppCAMO-iOS provides 14 security
technologies and is divided into static analysis prevention(Code Hardening)
technology and dynamic analysis prevention(RASP: Runtime Application Self
Protection) technology.
The static analysis prevention technology
of AppCAMO-iOS protects the xcarchive file from hacking, which includes
Name Obfuscation : It makes it difficult for hackers to analyze the source code by changing the source code. There are various technologies for obfuscation, and AppCAMO-iOS uses name obfuscation technology. Name obfuscation technology includes
class name obfuscation,
method name obfuscation,
field name obfuscation,
property name obfuscation,
category method name obfuscation,
category property name obfuscation,
protocol name obfuscation,
protocol method name obfuscation,
and protocol property name obfuscation.
These technologies prevent hackers from getting any information from identifiers by changing identifiers such as classes, methods, fields, properties, categories, category properties, protocols, protocol methods, and protocol properties to arbitrary values that have no meaning in the source code.
Usually, app developers give meaning to all of these identifiers to facilitate analysis and development of source code. For example, it is common to give the login screen a class name like "LoginActivity". This approach is good for analyzing and maintaining source code, but conversely, it makes it easy for hackers to analyze the source for malicious purposes. So, in name obfuscation provided by AppCAMO-iOS, the "LoginActivity" class name is changed to "a1234sfjkasf" so hacker can't know whether it is LoginActivity. Therefore, it can be said that the purpose is to make hackers give up or delay because it takes time to analyze the source code.
Name obfuscation changes the name of an identifier to a meaningless value. The part called by parsing module such as JSON that communicates with Server/DB and the dynamic class/method call part have been renamed with obfuscation technology, so errors may occur when running the iOS app. In this case, the user must directly input as a filter in the “obfuscation exclusion filter” so that name obfuscation is not applied. Name obfuscation can not be applied to the apps which use reflections described above.
String Encryption : It finds hard-coded strings such as server address, API key, user account, token, and etc in the source code of the app, and encrypts them. And it decrypts them only when the app is run in a secure environment. If a sensitive value such as a server address, an API key, a user account, or a token is exposed to a hacker, Not only can the server be attacked, but other secondary damage may occur. Therefore, this security technology option is recommended for all apps by default.
debug information
removal : It removes the relevant area on the IPA so that method parameter names, local variable names, and line numbers on the original source code are not exposed when an app is decompiled, and it makes source analysis more difficult.
The dynamic analysis prevention technology
of AppCAMO-iOS detects and blocks hacking attempts while the app is running,
which includes
Jailbreak Detection : It detects whether a device is jailbroken or not when running an app and prevents the app from running, if it is the jailbroken device.
Debugger Detection : It prevents the app from running if an app is being debugged.
Simulator Detection(Virtual Machine Detection) : It prevents the app from running if the app is run in a simulator.
 |
| Fig. 4 iOS app shielding solution AppCAMO-iOS security technologies |
Multiple Apps Management Technology
AppCAMO-iOS makes it easier to manage app
security technologies by providing management technologies such as user
management, project management, task management, bulletin boards and statistics
that are not available in other app security solutions. You can manage all
history of various app security technologies, from the beginning to the latest.
No SDK, No Coding, The Only One that can
provide GUI based Solution for easy to use
Unlike other solutions that require
learning time and coding using SDK or plug-in, AppCAMO does not require
learning time and coding to apply security technologies. AppCAMO is based on a
web GUI that allows users to intuitively select and apply various app security
technologies with just clicks.
 |
| Fig. 5 iOS App Security Solution AppCAMO-iOS Web Screen Layout |
Corporate Standard Mobile Application
Security Platform
In 2020, we built the iOS app security
standard platform for SKtelecom. AppCAMO-iOS is applied to more than 50 apps of
SKtelecom each year. This platform creates strategic R&D infrastructure
with SKtelecom security team which guarantees systematic customer feedback, new
requirements, stability, and credibility for AppCAMO-iOS.
 |
| Fig. 6 iOS App Security Standard Platform for a Mobile Carrier |
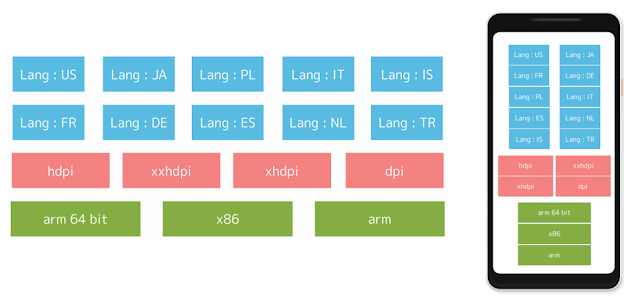
System Specifications
The required specifications of H/W and S/W
for the system structure and operation of the solution are as follows.
 |
| Fig. 6 iOS App Shielding Solution AppCAMO-iOS System Specifications |
AppCAMO-iOS Prerequsites
- Xcode Latest Version
- Bitcode enabled Archive Build
"AppCAMO-iOS provides multi-layered protection technology that fundamentally blocks app hacking, and has world-class app security technology by providing app hacking detection and prevention technology even at runtime. We are expanding our sales not only in Korea but also in overseas markets such as Southeast Asia."
If you are interested in this solution or have any questions, please feel free to contact us below.
Mail : appcamo@appcamo.com
Tel : +82-2-6951-3296
Home Page : www.appcamo.com